Finance and Technology
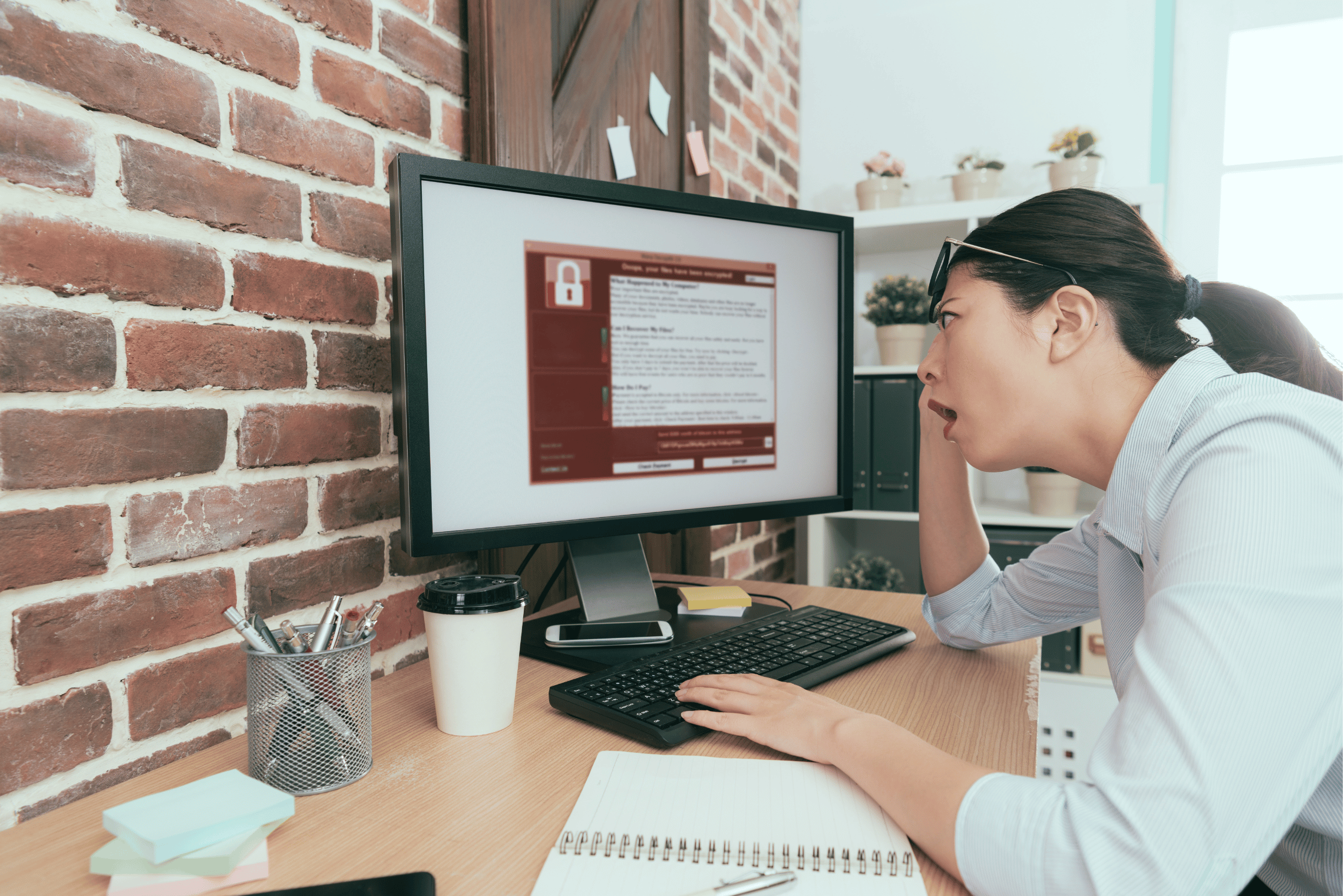
Protect Yourself from Malware Attacks: Myths about Cyber Security
Sep 2023 | By Greg Gazin
We protect our homes and businesses from crime, but when it comes to our computers and mobile devices, we tend to buy into myths, when, in fact, they could be causing us unnecessary grief.
Five Cyber Security Myths
1. There’s Nothing Important on my Computer
Most casual users insist that there isn’t anything worth having on their home computer. This may be true in the case of a complete computer malfunction, but whatever was lost can be recovered or recreated. Protecting it from cybercrime is not that simple. You may have visited an infected website or signed on to on-line banking from that computer. Email sent from that computer may have been compromised. This also applies to files or photos that were copied to, and from, that computer. Anything you shared with others could cause them to be infected and at risk.
2. Macs don’t get Viruses
You’d often hear this in the early days of personal computers. It might have been true, at one point in time. PC-based personal computers had the lion’s share of the market, so it made it more attractive to criminals. The Macintosh operating system, unlike a DOS or a Windows computer, had a closed architecture – making the challenge much more difficult.
A truer statement was that Macs couldn’t be infected by Windows’ viruses, because they ran different operation systems.
Fast forward to 2022. While both the Mac OS and iOS are highly secure, culprits still seem to find a way to get in, and can do so if you visit a fraudulent website or click a malicious link.
3. I’m careful, and only download from people that I know
It’s difficult to always be on alert. In a moment of haste or fatigue, you may click on something that you’d normally question. All it takes is one wrong move. As for family and friends, it’s not the same as quarantining with cohorts. They aren’t purposely trying to infect you, but they too, may have fallen victim. So, don’t make any assumptions.
4. You can’t get viruses on your phone
This is somewhat misinterpreted and can lead to a false sense of security. Due to the nature of mobile operating devices, it’s unlikely that a device will get a virus. However, since you can download files sent via malicious e-mails on your phone, click on links, and reach fraudulent websites, you can still be open to the same vulnerabilities caused by other types of malware.
With the millions of apps out there, you can also fall victim to fake apps or apps that contain malicious code. While apps from the Apple App Store, compared to their Google Play Android counterpart, are less likely to contain malware because of their stringent review process, an odd few still manage to sneak through.
And it makes it easier to get compromised with the proliferation in the use of QRCodes. They’re designed to make it easy to connect, link or download a file with a quick scan with our phone’s camera. We can’t see what the QRCode is or what it does until we scan it and sometimes this is done without a second thought of any potential consequences.
And with many mobile devices being used over unsecure public Wi-Fi, this also leaves users vulnerable to hacking or being compromised.
5. I have a virus protector, I should be fine
This is just one baby step in the right direction, but also a misconception. The big question one should ask is, “Do you have the right protection? Adequate protection for your environment? Across all your devices, and fully up-to-date?” and “Is your operating system also up to date?”
It’s a common misconception that anti-virus is a Swiss Army knife of cyber-protection. There is anti-virus protection that will protect you against viruses.
Some typical free programs usually have limited capacity, of course. Some will check if you have a virus but often of limited value after the fact, some may monitor in real time catching it before you’re infected.
However, malware takes many forms and there’s a lot more to be done. Some offerings also monitor in real-time incoming email, monitor for hacks and attacks on your network, and alert you of fake websites. Some offer a virtual private network (VPN) to allow you to create a private “tunnel” between your computer and where you’re connected to so you’re safe and secure. Others may offer email monitoring to see if your email address had been compromised and more.
The applications can usually be purchased individually, a la carte, or often in bundles. They may be called premium or deluxe, Internet Security or Total Security. They may be for home or business, computer or mobile or bundled together. They may also be designed for 1, 2, 5 or 10 devices.
Take the time to do your homework – of course you need to decide what’s best for you. Whatever you choose, it’s important to note that as malware is discovered, companies producing protection software update their offerings. Operating systems across all devices also require updates usually in the form of security patches.
Beware of malware myths. You’re only as strong as your weakest link.